Privateness
A primer on easy methods to use this highly effective instrument for uncovering and connecting info from publicly accessible sources
22 Jun 2023
•
,
4 min. learn

It’s a truism that non-public information is a helpful asset for cybercriminals, because it permits them to tailor and in any other case enhance their phishing and different social engineering assaults. The wealth and number of private information that’s accessible on-line is leveraged for assaults and scams that focus on not solely folks but in addition corporations.
However organizations can also faucet into strategies corresponding to Open Source Intelligence (OSINT) that permit them to see their community the best way attackers may see it and to assemble varied sorts of publicly accessible details about themselves in an effort to establish their weak factors and finally improve their safety. One such in style and highly effective information-gathering instrument is a bit of software program known as Maltego.
What’s Maltego and why use it?
Maltese is a bit of software program that enables moral hackers, penetration testers and different safety practitioners to uncover details about folks or corporations on the web. It permits them to cross-match information and map out connections between social media profiles, electronic mail addresses, telephone numbers, places, skilled affiliations and different info. The knowledge is represented in easy-to-digest graphical hyperlinks and relationship diagrams.
Learn additionally: 5 free OSINT tools for social media
Maltego provides a slew of advantages for varied entities, each within the non-public and public sectors. Cybersecurity practitioners can leverage Maltego for gathering helpful details about threats which may jeopardize the safety of an organization’s info and infrastructure. Legislation enforcement companies can use Maltego to gather helpful information that helps in investigating fraud and gathering digital proof, amongst different issues.
What sort of knowledge can Maltego acquire?
The instrument’s most-used options are these that allow you to establish and visualize relationships between what the instrument calls entities, corresponding to IP addresses, domains, e-mails, social media profiles, and many others. As well as, Maltego means that you can combine completely different sources of knowledge, corresponding to databases, on-line search instruments, APIs, and many others.
Even Maltego’s free model fetches a considerable amount of info, together with:
- Community info: Maltego can scan and collect details about community hosts, open ports and protocols used. For instance, with Maltego, you’ll be able to obtain Shodan throughout the instrument, which lets you collect extra particular details about the community to be analyzed.
- Area and electronic mail info: Maltego can collect details about domains, corresponding to our DNS entries, electronic mail logs, and host title logs. It could additionally collect details about electronic mail addresses, domains, electronic mail suppliers and DNS information.
- Social media info: You will get Maltego to gather varied sorts of knowledge from social media, together with profiles, posts, buddies, followers and connections.
- Details about folks and organizations: Maltego can collect details about folks or organizations, together with their names, addresses, phone numbers, electronic mail addresses, web sites and social media profiles.
- Malware info: Maltego can collect details about malware, corresponding to file names, fingerprints, assault patterns and habits. This helps collect details about threats, making it a helpful instrument for menace intelligence duties.
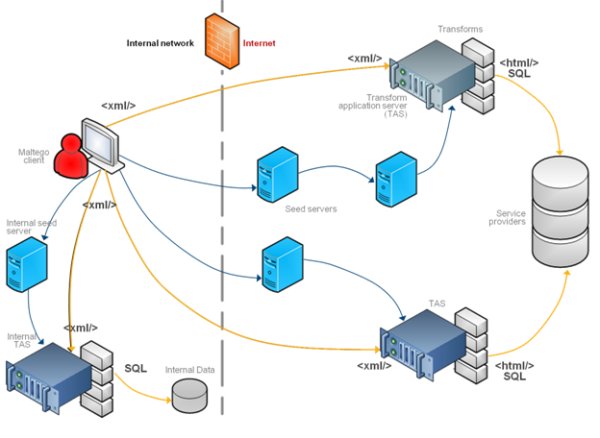
Right here’s what occurs underneath the hood:
- The Maltego shopper sends a request in XML format to seed servers over HTTPS.
- The request from the seed server is distributed to remodel utility servers (TAS) that, in flip, ahead it to the service suppliers.
- The outcomes are despatched to the Maltego shopper.
Easy methods to use Maltego
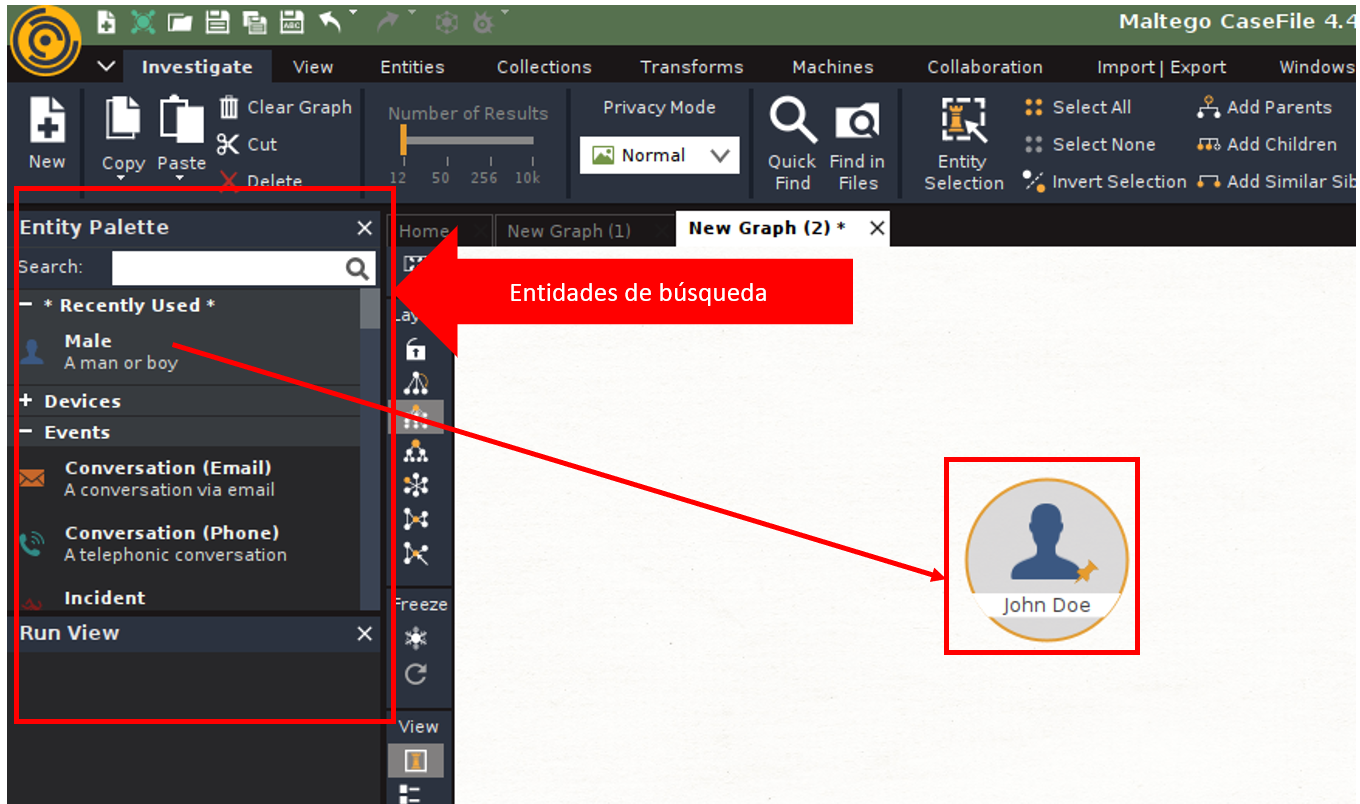
Download and install Maltego on Home windows, macOS or Linux and create an account on the instrument’s web site that can can help you use the app and the free servers. As soon as you put in the software program and check in, you need to create a brand new search web page and drag the entity there (i.e., the kind of search you need to make – on this case, an individual) to then run the search and see the outcomes.
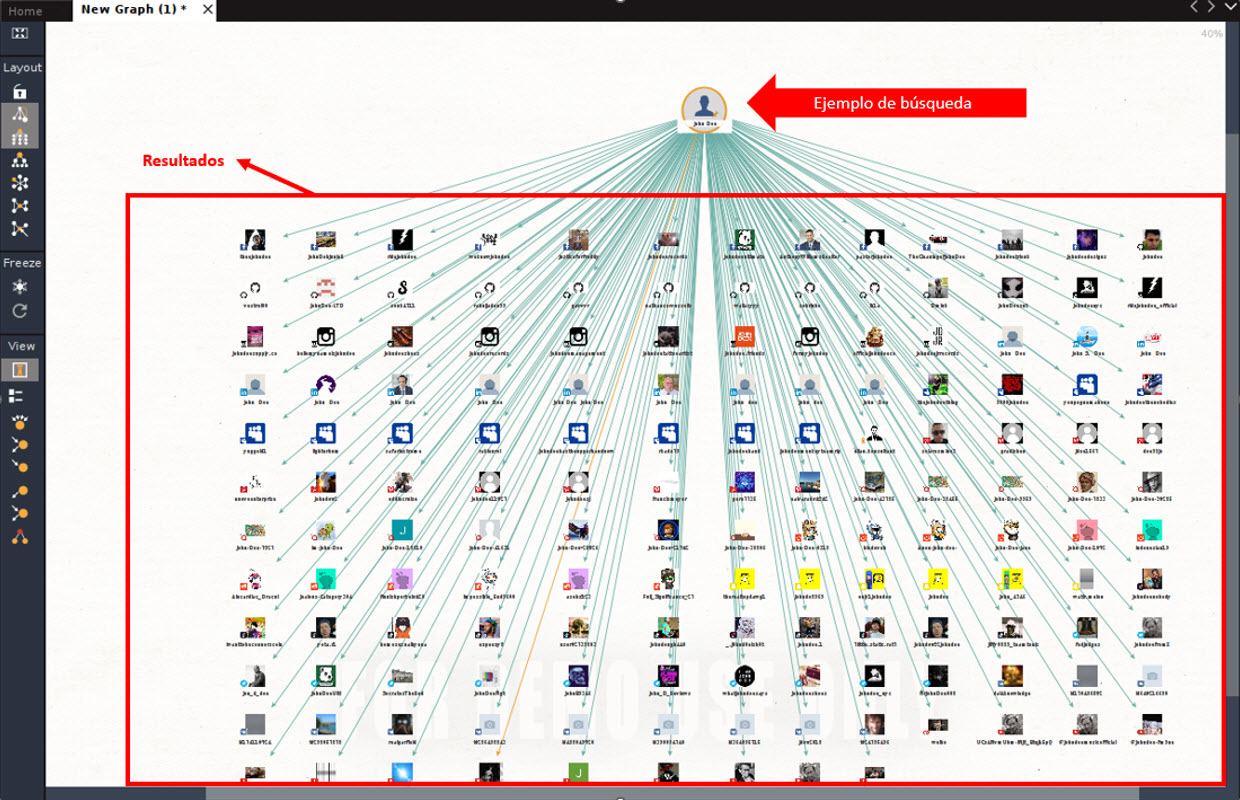
Upon getting chosen the kind of search you need to make, double click on on the particular person icon to entry the configuration part and, when you enter the title, good click on on the particular person icon and choose “run transform”. Inside this class, there are completely different subcategories, the place you’ll be able to seek for particular info, corresponding to electronic mail addresses, IP addresses of a web site, and many others. On this explicit case, we’ll use the “all transforms” choice to seek for all potential info within the Web, so it is going to rapidly begin gathering information and the outcome will likely be much like that proven within the picture beneath:
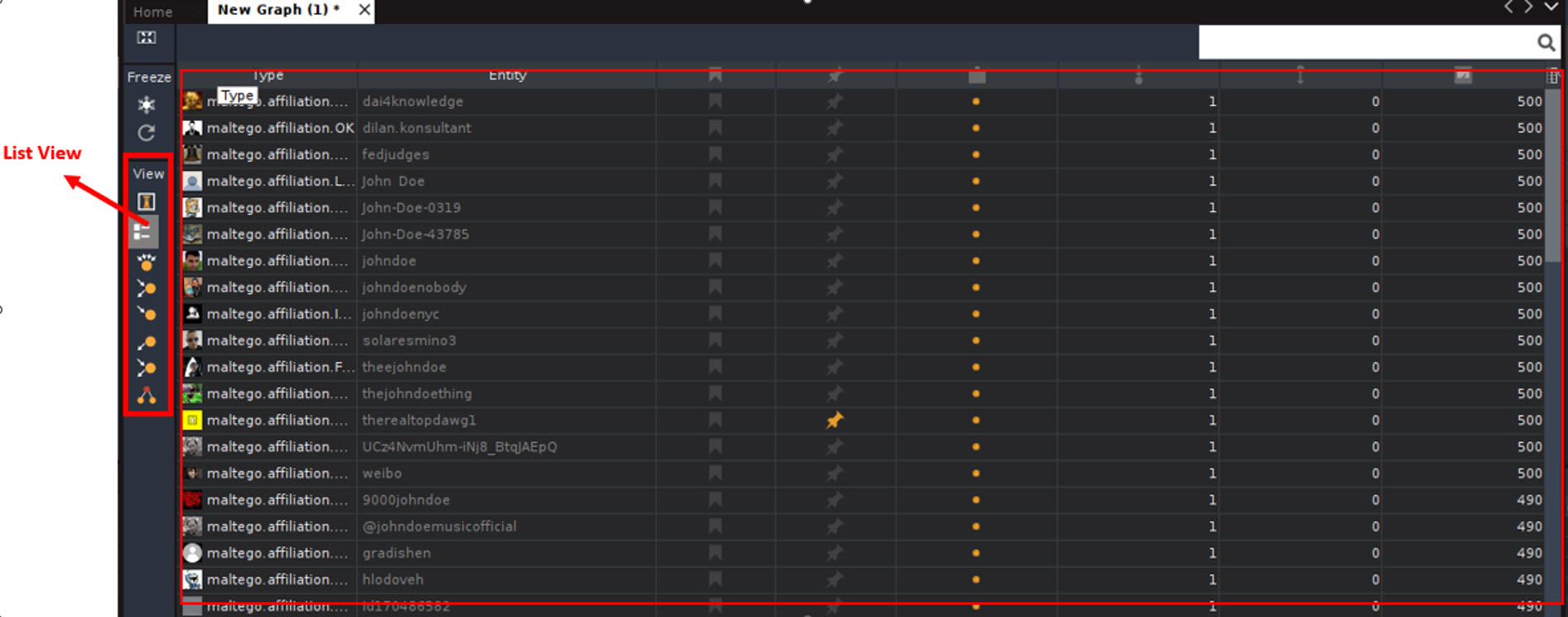
Within the screenshot, you’ll be able to see web sites the place the title “John Doe” was talked about or there may be info associated to it. It’s price mentioning that this instrument is so highly effective that it could discover profiles in Fb, LinkedIn, Instagram, Tik Tok, Snapchat, Twitter, and Youtube, amongst others. However that’s not all, as you may as well discover buddies associated to this particular person in social media. To see it in additional element, click on on the “List View” button within the “View” lateral bar, the place you’ll be able to see the hyperlinks and different info.
Conclusion
The knowledge gathered utilizing Maltego can be utilized by cybercriminals when deploying their assaults. For this reason it’s helpful to know what sort of info a cybercriminal can study us or our firm and be cognizant of – and probably lower – our stage of publicity.
It goes with out saying that everytime you use an OSINT instrument, be sure to are conscious of native and nationwide legal guidelines and rules associated to the gathering and use of knowledge in order that you don’t commit against the law or violate the privateness of others. Additionally, when gathering and storing info, you will need to take measures to guard it towards potential theft or information breaches.
Author:
Date: 2023-06-22 07:30:27