Cybersecurity researchers have found a recent batch of malicious packages within the npm bundle registry which are designed to exfiltrate Kubernetes configurations and SSH keys from compromised machines to a distant server.
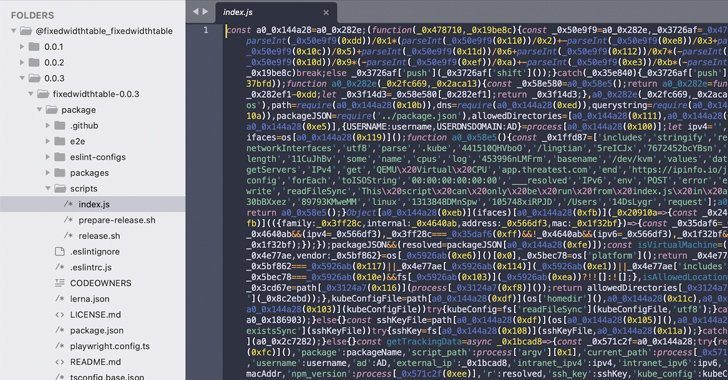
Sonatype mentioned it has found 14 totally different npm packages to date: @am-fe/hooks, @am-fe/supplier, @am-fe/request, @am-fe/utils, @am-fe/watermark, @am-fe/watermark-core, @dynamic-form-components/mui, @dynamic-form-components/shineout, @expue/app, @fixedwidthtable/fixedwidthtable, @soc-fe/use, @spgy/eslint-plugin-spgy-fe, @virtualsearchtable/virtualsearchtable, and shineouts.
“These packages […] attempt to impersonate JavaScript libraries and components, such as ESLint plugins and TypeScript SDK tools,” the software program provide chain safety agency said. “But, upon installation, multiple versions of the packages were seen running obfuscated code to collect and siphon sensitive files from the target machine.”

Together with Kubernetes config and SSH keys, the modules are additionally able to harvesting system metadata corresponding to username, IP handle, and hostname, all of that are transmitted to a website named app.threatest[.]com.
The disclosure comes just a little over per week after Sonatype detected counterfeit npm packages that exploit a way referred to as dependency confusion to impersonate inside packages purportedly utilized by PayPal Zettle and Airbnb builders as a part of an moral analysis experiment.
That mentioned, menace actors continue to target open-source registries like npm and PyPI with cryptojackers, infostealers, and different novel malware to compromise developer programs and finally poison the software program provide chain.
In a single occasion highlighted by Phylum earlier this month, an npm module named hardhat-gas-report remained benign for greater than eight months since January 6, 2023, earlier than receiving two back-to-back updates on September 1, 2023, to incorporate malicious JavaScript able to exfiltrating Ethereum non-public keys copied to the clipboard to a distant server.
“This targeted approach indicates a sophisticated understanding of cryptocurrency security and suggests that the attacker is aiming to capture and exfiltrate sensitive cryptographic keys for unauthorized access to Ethereum wallets or other secured digital assets,” the corporate said.
Level-Up SaaS Security: A Comprehensive Guide to ITDR and SSPM
Keep forward with actionable insights on how ITDR identifies and mitigates threats. Study in regards to the indispensable function of SSPM in guaranteeing your id stays unbreachable.
One other case of an attempted supply chain attack entails a artful npm bundle referred to as gcc-patch that masquerades as a bespoke GCC compiler however truly harbors a cryptocurrency miner that “covertly taps into the computational power of innocent developers, aiming to profit at their expense.”
What’s extra, such campaigns have diversified to span the Javascript (npm), Python (PyPI) and Ruby (RubyGems) ecosystems, what with menace actors importing a number of packages with information assortment and exfiltration capabilities and following it up by publishing new variations carrying malicious payloads.
The marketing campaign particularly targets Apple macOS customers, indicating that malware in open-source bundle repositories isn’t solely turning into more and more prevalent, however are additionally singling out different working programs past Home windows.
“The author of these packages is staging a broad campaign against software developers,” Phylum noted in an evaluation. “The end goal of this campaign remains unclear.”