Understanding Injection Vulnerabilities
Injection vulnerabilities exist when data offered by customers of the appliance isn’t correctly validated or sanitized earlier than it’s used. Within the case of Cross-Website Scripting, this may imply {that a} area permits the entry of JavaScript which is then re-displayed to the consumer. For SQL injection, this implies a area that’s written to the database isn’t correctly validated and a SQL sanitization perform isn’t run in opposition to the information earlier than it’s despatched to the database as a part of a command for execution. The final vulnerability they enumerate is “External Control of File Name or Path” because of this a area permits the consumer to insert a file title or a path that’s used to jot down or learn from the underlying working system on the server. In every case, now we have lacking information validation. So, for our working definition let’s go along with this:
Injection vulnerabilities are lacking validations and sanitizations of consumer enter that permit a consumer to achieve entry to extra information than they need to.
Catching Lacking Validations and Sanitizations in Code Evaluate
Lacking validation and sanitization of inputs will not be easy to search out by means of automated testing, and they don’t seem to be constantly discovered by means of click on testing of purposes earlier than deployment. Most testers will not be sufficiently educated in assault vectors to search out these issues, and plenty of are hidden away in APIs or could also be obscured by client-side information validation. As soon as you recognize what to search for, although, these vulnerabilities soar off the display in a code evaluation.
Catching JavaScript Injection Vulnerabilities
JavaScript injection vulnerabilities, the related part of Cross-Website Scripting, occur most ceaselessly when a textual content enter area is written to the database after which displayed later with none sanitization of the displayed data. So, what sanitization do we’d like right here? Primarily we have to flip sure particular characters into their entity-encoding earlier than show.
So, if somebody inputs this right into a textual content field:
After we write it again out to the web page we wish to flip it into this:
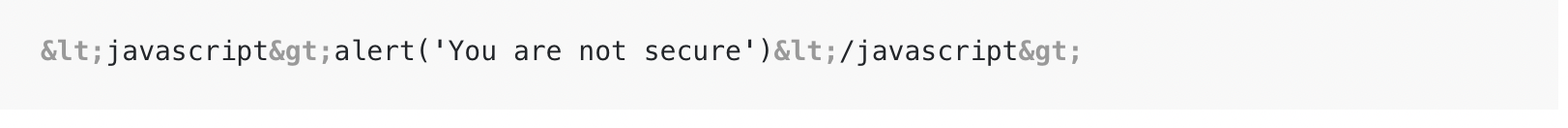
The greater-than and less-than symbols have been became their HTML entity equivalents, so this is not going to be interpreted as HTML and the JavaScript perform enclosed gained’t be executed.
Totally different languages have completely different strategies for escaping HTML. Studying up on these strategies will assist put together you. In Ruby, I do know to search for the next telltale indicators:
- Utilizing the
.html_safeperform in Rails views. - Not utilizing
CGI::escapeHTMLoutside-of-view contexts with auto-escaping. - Utilizing uncooked markdown compiled with out defending in opposition to JavaScript tag injection.
Relying on the language, you’ll discover many alternative telltale indicators of JavaScript injection vulnerabilities that can lead to Cross-Website Scripting. Turn into acquainted with the HTML escaping system within the language you’re utilizing day-to-day, and also you’ll discover your personal checklist to search for.
Catching SQL Injection Vulnerabilities
SQL injection vulnerabilities happen when strings from the consumer are inserted immediately right into a SQL assertion with out first being sanitized. The commonest means that this occurs is string interpolation.
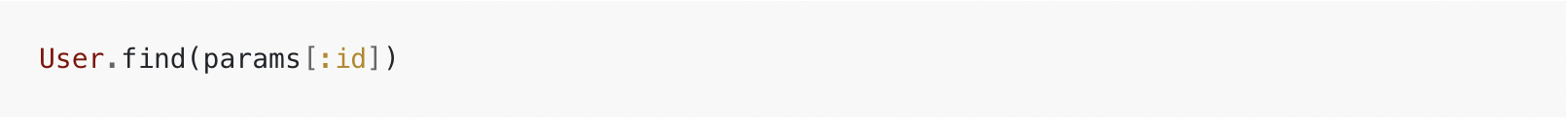
In Ruby, for instance, the next code is insecure:

It’s because the ID parameter might be changed with any string the consumer needs and it will likely be inserted immediately into the SQL assertion with none escaping. The safe model would leverage the ORM to carry out the identical question:
Utilizing ORMs accurately will usually take away any threat of SQL injection, although the right method differs from ORM to ORM. In ActiveRecord, there are strategies that take further arguments that permit data to be safely inserted into SQL strings.
For instance:
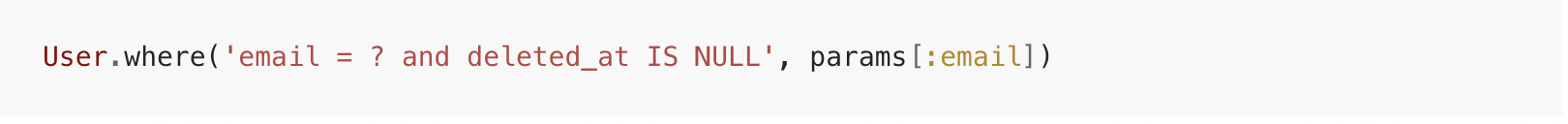
The query mark syntax signifies to the ORM the place to insert the escaped model of the second parameter. Most different ORMs will present comparable performance but it surely’s good apply to grasp how a lot sanitization is taken care of on the ORM stage and the ORM’s limits in dealing with sanitization.
The largest purple flag to search for in code evaluation is string interpolation being utilized in SQL queries. That is usually unsafe.
Catching Exterior Management of File Paths
Exterior management of file paths is one thing that crops up when customers are allowed to add a file or initialize a useful resource server-side, reminiscent of a SQLite database. It will probably additionally occur on studying if a system isn’t configured correctly to solely learn from sure areas.
The hazard in permitting the consumer to regulate the trail is that they’ll try to jot down information to harmful locations, or acquire entry to the contents of supply code or different information that comprise privileged data.
Catching one of these safety difficulty requires that the programmer or reviewer concentrate on cases the place a file path might be inserted right into a parameter—this may very well be one thing easy like a file add path or file learn command, or someplace barely extra sudden reminiscent of a database connection string.
I search for cases the place this data is handed in as a full path moderately than as a sub-path of a containing folder or the safer route of saving off the supposed path to the database however writing the file to a random location on disk to keep away from attainable safety points.
Conclusion
Injection vulnerabilities end result from insecure dealing with of consumer inputs. They’re comparatively easy to repair as soon as the underlying points that trigger them are understood, and are ceaselessly discovered by skilled reviewers who know what to search for. The prevalence of injection vulnerabilities right now is among the finest arguments for persevering with to carry out code evaluation in lots of organizations—one of these vulnerability is most ceaselessly caught by means of human inspection of the offending code.
This submit was initially revealed on the PullRequest web site. On April twenty eighth, 2022 HackerOne acquired PullRequest to assist energy developer-first safety testing options.
Discover submit creator Will Barrett here.
Author: William Barrett
Date: 2022-06-09 12:00:00
.png)


