Biometric identification expertise has developed considerably over time. Initially, biometric identification was used primarily for large-scale authorities tasks equivalent to nationwide ID playing cards, passports, and regulation enforcement. The expertise was complicated and costly, making it inaccessible to the typical enterprise group. Nonetheless, because the demand for safer types of identification grew, the expertise turned extra accessible and reasonably priced.
In the present day, biometric identification is utilized in many purposes, together with border controlbanking, healthcare, and even most enterprises use biometric identification to handle their workforce. The expertise has turn into rather more user-friendly, with many biometric identification techniques counting on the iris, facial recognition, and fingerprint scanning. Biometric identification is now extra accessible to builders, with many biometric APIs out there for integration into a variety of purposes. Consequently, the usage of biometric identification is turning into more and more widespread. It’s anticipated to proceed to develop within the coming years. This weblog will give a step-by-step course of so as to add biometric performance to any net software.
Biometric Seize Device & Matching Engine
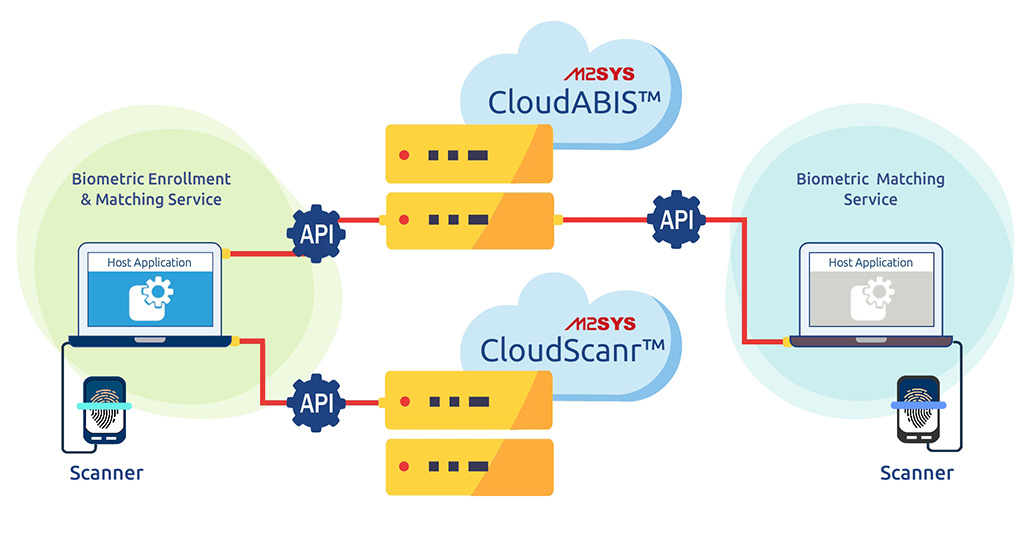
Integrating biometric performance into an online software requires a biometric machine, a biometric capture tooland a biometric matching engine. On this context, CloudScanr will function the biometric seize device, CloudABIS because the biometric matching engine, and the Jail safe software from M2SYS eGov shall be used to exhibit the combination course of. To be able to proceed with the setup, you will need to acquire a basic understanding of each the biometric seize device and the matching engine.
Biometric Seize Device: You need to use any biometric machine to seize your biometric knowledge. As soon as the seize device completes biometric knowledge capturing, the seize device will provoke the API name and ship the seize knowledge to the biometric matching servers together with the required parameters. M2SYS CloudScanr is a dynamic seize device that simplifies the method of integrating biometric {hardware} into net purposes, eliminating the necessity for builders to fret about ActiveX, native code integration, or browser plug-ins. CloudScanr makes use of a web-based API that lets you combine capturing from numerous biometric units into any home windows or web-based software. It automates the power to seize numerous sorts of biometric templates and picture codecs into a really simple-to-use framework. With CloudScanr, the most well-liked biometric units may be simply built-in, offering a seamless “plug and play” expertise for the consumer.
Biometric Matching Engine: A biometric matching engine is an important software program part that compares and matches biometric knowledge with already enrolled templates saved within the database. The matching engine’s predominant goal is to match a person’s identification by figuring out if the biometric knowledge collected from them matches the already enrolled template saved within the database. CloudABIS is a strong and scalable biometric identification system provided as a service (BaaS) that eliminates the challenges and bills related to developing and sustaining a dependable biometric identification system. It helps multimodal matching with a single API name and all of the consumer knowledge is totally safe towards numerous cyberattacks.
To configure CloudABIS biometric API along with your net software, please comply with these easy steps:
Setting Up CloudABIS Account
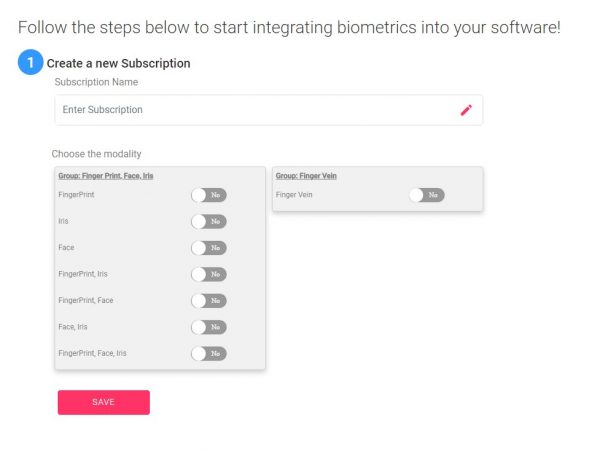
To start out, the consumer should first create an account on the CloudABIS portal. As soon as the registration course of is full, the consumer shall be directed to a web page the place they need to choose the popular biometric modality for his or her mission. It’s then vital to call the mission and reserve it for future reference.
Accumulate the Biometric Credential
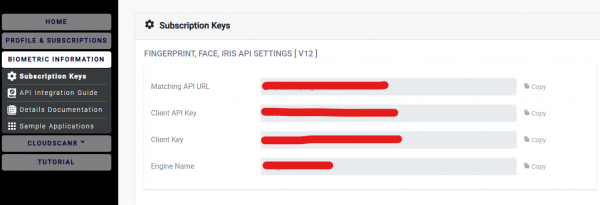
As soon as an account is created, customers shall be given a 14-day trial interval to check the software program and decide whether or not they wish to subscribe to CloudABIS based mostly on their mission or enterprise wants. To configure the appliance, customers should first get hold of their biometric credentials, together with the Matching API URL, Shopper API KEY, and the Shopper KEY. These credentials may be obtained by clicking on the ‘Biometric Information’ tab and choosing ‘Subscription Keys’.
Obtain CloudScanr Seize Device
Customers can seamlessly combine any biometric machine with their Home windows PC by downloading CloudScanr from the CloudABIS portal and putting in it. As soon as CloudScanr is put in, customers can simply join their desired biometric machine to their PC, choose the machine from CloudScanr, and reserve it. CloudScanr will care for the remainder by routinely putting in the required driver and integrating the machine for fast use.
Configure the Software with Biometric Credential
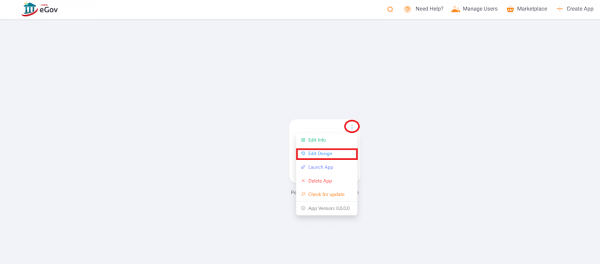
To configure and take a look at the biometric credentials, we’ll make the most of the M2SYS jail safe software. Step one is to obtain the appliance from the M2SYS eGov Marketplace. As soon as downloaded, customers ought to click on on the appliance icon and choose “Edit Design” by clicking on the three dots.
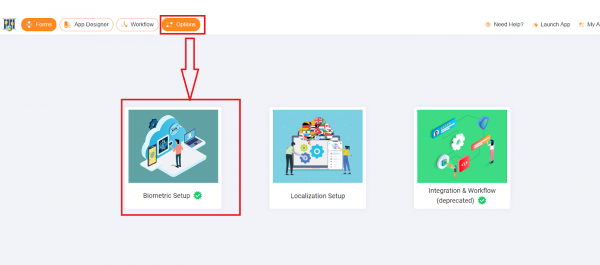
As soon as the “Edit Design” button is clicked, the Software Designer will open up. Customers ought to then navigate to the “Options” tab and choose “Biometric Setup” to proceed.
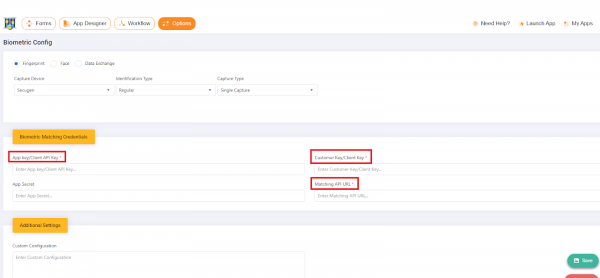
On the Biometric Setup menu, customers are required to pick the required machine or modality they are going to be utilizing, and configure the biometrics from this part. To take action, customers want to repeat and paste the biometric matching credential obtained from the CloudABIS portal. As soon as the credentials have been inputted, customers ought to click on the “Save” button to finish the setup course of.
After inputting the credentials, click on save.
Register Biometric
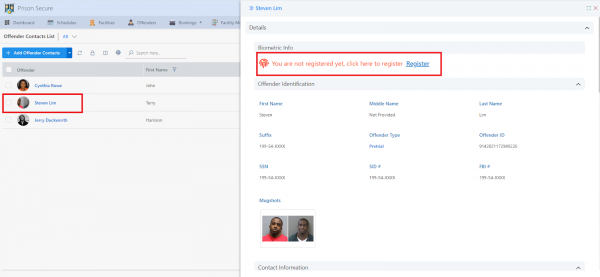
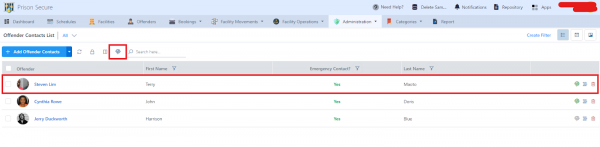
Since we’re utilizing a safe jail software from M2SYS eGov, we might want to register the biometrics of an offender. This may be executed by clicking on the “Administrator” button positioned within the higher menu and choosing the “Offender Contact List.” From there, customers can choose the title of the offender they want to register, and if the particular person just isn’t but registered with biometrics, they’ll click on on the “Register” button.
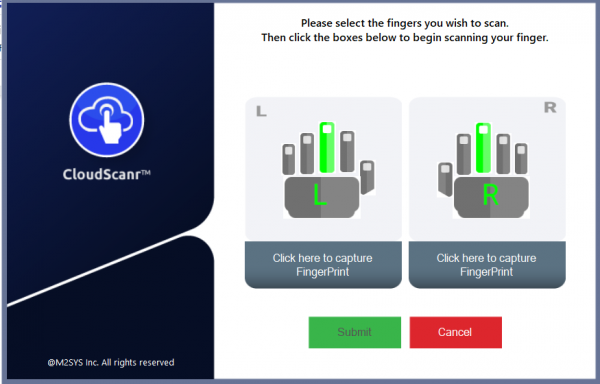
It will set off an API name to CloudScanr, which can provoke the biometric seize course of. As soon as the biometric knowledge is captured and is transformed to a base64 template, it should provoke an API name to ship the captured knowledge to CloudABIS API, together with the required parameters. Based mostly on the request obtained, the seize device will then talk the corresponding response again to the appliance.
 Establish Customers
Establish Customers
Using biometrics, the administrator can establish people with precision by performing quite a few 1:N searches. The identification course of by the Jail safe app is easy. Click on on the biometric icon from the offender contact checklist, and the app will provoke the biometric seize course of by making an API name to the seize device. The captured biometric knowledge shall be transformed right into a base64 template and despatched to CloudABIS API by one other API name. CloudABIS will seek for the template in its saved database and return the outcomes to the appliance.
We hope that the steps outlined above will help you in implementing biometric performance in your net platform. Do you have to encounter any points throughout the configuration course of or have any queries, please don’t hesitate to contact us
Author: Stanly Palma
Date: 2023-02-14 05:47:56