Malicious adverts served inside Microsoft Bing’s synthetic intelligence (AI) chatbot are getting used to distribute malware when trying to find in style instruments.
The findings come from Malwarebytes, which revealed that unsuspecting customers may be tricked into visiting booby-trapped websites and putting in malware straight from Bing Chat conversations.
Launched by Microsoft in February 2023, Bing Chat is an interactive search experience that is powered by OpenAI’s massive language mannequin referred to as GPT-4. A month later, the tech big began exploring inserting adverts within the conversations.
However the transfer has additionally opened the doorways for menace actors who resort to malvertising techniques and propagate malware.
“Ads can be inserted into a Bing Chat conversation in various ways,” Jérôme Segura, director of menace intelligence at Malwarebytes, said. “One of those is when a user hovers over a link and an ad is displayed first before the organic result.”

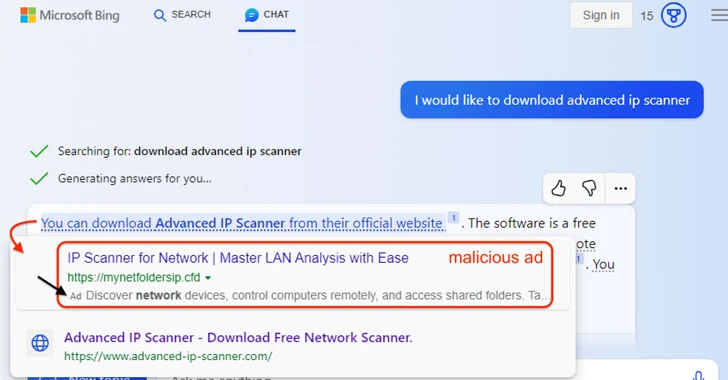
In an instance highlighted by the cybersecurity vendor, a Bing Chat question to obtain a authentic software program referred to as Superior IP Scanner returned a hyperlink that, when hovered, displayed a malicious advert pointing to a fraudulent hyperlink earlier than the official website internet hosting the software.
Clicking the hyperlink takes the person to a visitors course system (TDS) that fingerprints and determines if the request is definitely originating from an actual human (versus a bot, crawler, or sandbox), earlier than taking them to a decoy web page containing the rogue installer.
The installer is configured to run a Visible Fundamental Script that beacons to an exterior server with the seemingly purpose of receiving the next-stage payload. The precise nature of the malware delivered is presently unknown.
A notable facet of the marketing campaign is that the menace actor managed to infiltrate the advert account of a authentic Australian enterprise and create the adverts.
“Threat actors continue to leverage search ads to redirect users to malicious sites hosting malware,” Segura stated. “With convincing landing pages, victims can easily be tricked into downloading malware and be none the wiser.”
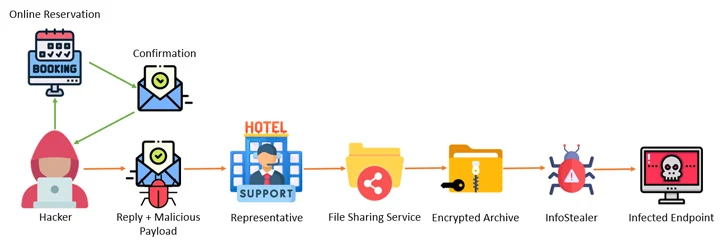
The revelation comes as Akamai and Perception Point uncovered a multi-step campaign that entails attacking the programs of accommodations, reserving websites, and journey companies with info stealer malware after which leveraging the entry to the accounts to go after monetary knowledge belonging to prospects utilizing pretend reservation pages.
“The attacker, masquerading as the hotel, reaches out to the customer through the booking site, urging the customer to ‘re-confirm their credit card,’ then steals the customer’s information,” Akamai researcher Shiran Guez stated, noting how the assaults prey on the sufferer’s sense of urgency to drag off the operation.
Fight AI with AI — Battling Cyber Threats with Next-Gen AI Tools
Able to deal with new AI-driven cybersecurity challenges? Be a part of our insightful webinar with Zscaler to deal with the rising menace of generative AI in cybersecurity.
Cofense, in a report printed this week, stated the hospitality sector has been on the receiving finish of a “well-crafted and innovative social engineering attack” that is designed to ship stealer malware equivalent to Lumma Stealer, RedLine Stealer, Stealc, Spidey Bot, and Vidar.
“As of now, the campaign only targets the hospitality sector, primarily targeting luxury hotel chains and resorts, and uses lures relative to that sector such as booking requests, reservation changes, and special requests,” Cofense said.
“The lures for both the reconnaissance and phishing emails match accordingly and are well thought out.”
The enterprise phishing menace administration agency stated it additionally observed malicious HTML attachments supposed to hold out Browser-in-the-Browser (BitB) assaults by serving seemingly innocuous pop-up home windows that entice electronic mail recipients into offering their Microsoft credentials.
The discoveries are an indication that menace actors are consistently discovering new methods to infiltrate unwitting targets. Customers ought to keep away from clicking on unsolicited hyperlinks, even when they give the impression of being authentic, be suspicious of pressing or threatening messages asking for quick motion, and verify URLs for indicators of deception.
Author: information@thehackernews.com (The Hacker Information)
Date: 2023-09-29 05:13:00