A vital zero-day vulnerability in all variations of Exim mail switch agent (MTA) software program can let unauthenticated attackers acquire distant code execution (RCE) on Web-exposed servers.
Discovered by an nameless safety researcher and disclosed by means of Development Micro’s Zero Day Initiative (ZDI), the safety bug (CVE-2023-42115) is because of an Out-of-bounds Write weak point discovered within the SMTP service.
Whereas any such subject can result in software program crashes or corruption of information following profitable exploitation, it can be abused by attackers for code or command execution on weak servers.
“The specific flaw exists within the smtp service, which listens on TCP port 25 by default,” a ZDI security advisory revealed on Wednesday explains.
“The issue results from the lack of proper validation of user-supplied data, which can result in a write past the end of a buffer. An attacker can leverage this vulnerability to execute code in the context of the service account.”
Whereas ZDI reported the vulnerability to the Exim workforce in June 2022 and resent information on the flaw on the vendor’s request in Might 2023, the builders failed to offer an replace on their patch progress.
Because of this, ZDI revealed an advisory on September 27, with particulars on the CVE-2023-42115 zero-day and a full timeline of all exchanges with the Exim workforce.
Tens of millions of servers uncovered to assaults
MTA servers like Exim are extremely weak targets, primarily as a result of they’re typically accessible by way of the Web, serving as simple entry factors for attackers right into a goal’s community.
The Nationwide Safety Company (NSA) stated three years in the past, in Might 2020, that the infamous Russian navy hacking group Sandworm has been exploiting the critical CVE-2019-10149 (The Return of the WIZard) Exim flaw since at the very least August 2019.
Exim can also be the default MTA on Debian Linux distros and the world’s hottest MTA software program, based on a mail server survey from September 2023.
In response to the survey, Exim is put in on greater than 56% out of a complete of 602,000 mail servers reachable on the Web, representing simply over 342,000 Exim servers.
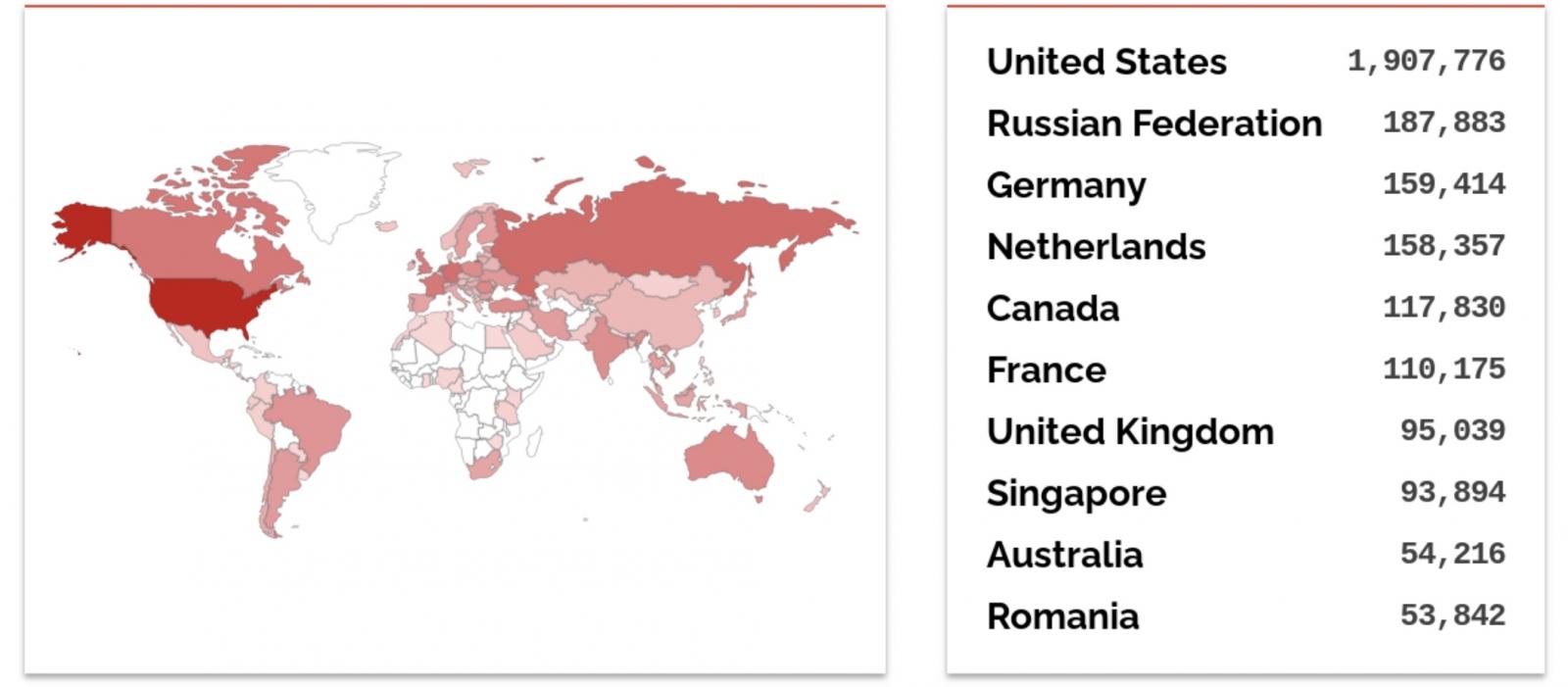
Simply over 3.5 million Exim servers are at present uncovered on-line per a Shodan searchmost of them in the US, adopted by Russia and Germany.
Whereas a patch is just not but out there to safe weak Exim servers in opposition to potential assaults, ZDI suggested admins to limit distant entry from the Web to thwart incoming exploitation makes an attempt.
“Given the nature of the vulnerability, the only salient mitigation strategy is to restrict interaction with the application,” ZDI warned.
Authentic Submit URL: https://www.bleepingcomputer.com/information/safety/millions-of-exim-mail-servers-exposed-to-zero-day-rce-attacks/
Author:
Date: 2023-09-29 23:46:06



