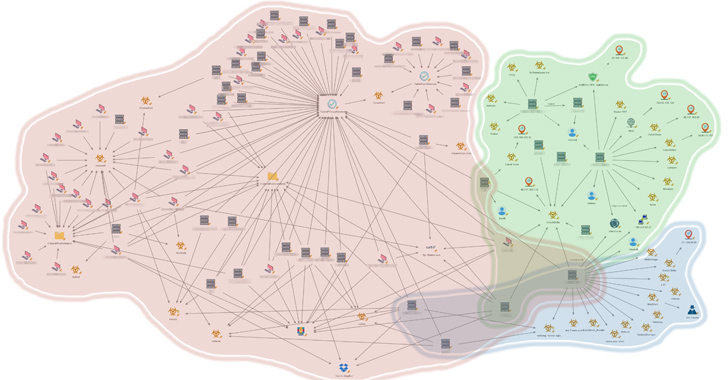
An unnamed Southeast Asian authorities has been focused by a number of China-nexus risk actors as a part of espionage campaigns focusing on the area over prolonged durations of time.
“While this activity occurred around the same time and in some instances even simultaneously on the same victims’ machines, each cluster is characterized by distinct tools, modus operandi, and infrastructure,” Palo Alto Networks Unit 42 researchers Lior Rochberger, Tom Fakterman, and Robert Falcone said in an exhaustive three-part report.
The assaults, which focused completely different governmental entities equivalent to vital infrastructure, public healthcare establishments, public monetary directors and ministries, have been attributed with reasonable confidence to 3 disparate clusters tracked as Stately Taurus (aka Mustang Panda), Alloy Taurus (aka Granite Hurricane), and gelsemium.
Mustang Panda Makes use of TONESHELL Variant and ShadowPad
“The attackers conducted a cyberespionage operation that focused on gathering intelligence as well as stealing sensitive documents and information, while maintaining a persistent and clandestine foothold,” the researchers saiddescribing it as “highly-targeted and intelligence-driven.”
The exercise spanned from the second quarter of 2021 to the third quarter of 2023, leveraging an assortment of instruments to conduct reconnaissance, steal credentials, keep entry, and conduct post-compromise actions.

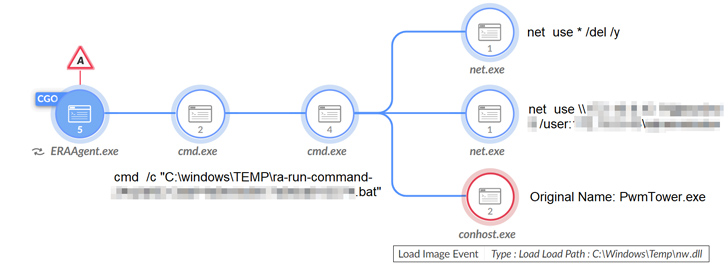
A few of the notable software program used to achieve these targets comprise the LadonGo open-source scanning framework, AdFind, Mimikatz, Impacket, China Chopper net shells, Cobalt Strike, ShadowPadand a brand new model of the TONESHELL backdoor.
The malware eschews using shellcode in favor of three DLL-based elements to arrange persistence on the endpoint, set up command-and-control communications with a distant server, and perform information-gathering operations, together with command execution, file system interplay, keylogging, and display seize.
“During the operation, the threat actor slowly took control of the victims’ environments, focusing on maintaining control for a long-term operation,” the researchers famous. “The purpose of the threat actor’s efforts appears to be the continuous gathering and exfiltration of sensitive documents and intelligence.”
Alloy Taurus Goals to Fly Underneath the Radar
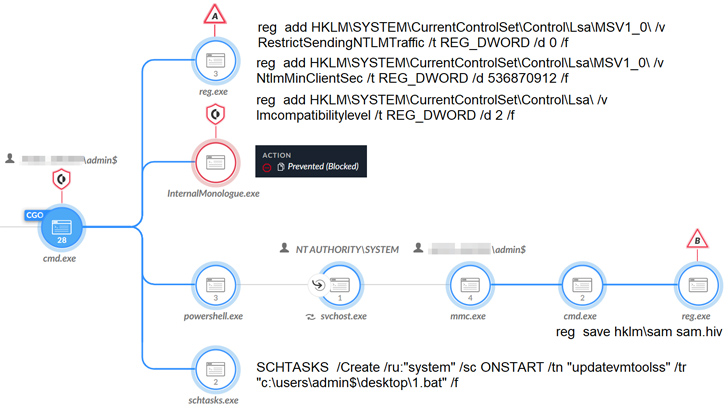
The intrusion set linked to Alloy Taurus is claimed to have commenced in early 2022 and continued all through 2023, leveraging unusual methods and bypassing safety merchandise for long-term persistence and reconnaissance.
These assaults, occurring in six completely different waves, weaponize safety flaws in Microsoft Alternate Servers to deploy net shells, which then serves as a conduit to ship further payloads, counting two beforehand unknown .NET backdoors Zapoa and ReShell to execute arbitrary instructions remotely and harvest delicate information.
Zapoa additionally incorporates options to extract system data, run shellcode, enumerate working processes, load extra .NET meeting recordsdata to reinforce its capabilities, and timestamp recordsdata and artifacts with a equipped date, a method referred to as timestomping.
“The threat actor behind this cluster employed a mature approach, utilizing multiwave intrusions and exploiting vulnerabilities in Exchange Servers as their main penetration vector,” the researchers said.
In some instances, Alloy Taurus has additionally been noticed finishing up credential theft to facilitate lateral motion by abusing the distant administration device AnyDesk already current within the infiltrated atmosphere.
Fight AI with AI — Battling Cyber Threats with Next-Gen AI Tools
Able to sort out new AI-driven cybersecurity challenges? Be a part of our insightful webinar with Zscaler to deal with the rising risk of generative AI in cybersecurity.
A few of the different software program put in by the risk actor embody Cobalt Strike, Quasar RATHDoor (a backdoor beforehand utilized by Chinese language teams like Naikon and Goblin Panda), a Gh0st RAT variant often known as Gh0stCringeand Winntia multi-functional implant able to granting distant management to an contaminated machine.
Gelsemium Singles Out Susceptible IIS Servers
“This unique cluster had activity spanning over six months between 2022-2023,” the researchers noted.
“It featured a combination of rare tools and techniques that the threat actor leveraged to gain a clandestine foothold and collect intelligence from sensitive IIS servers belonging to a government entity in Southeast Asia.”
The assault chains capitalize on susceptible net servers to put in net shells and distribute backdoors like OwlProxy and SessionManager, whereas concurrently using different instruments equivalent to Cobalt Strike, Meterpreter, Earthwormand SpoolFool for post-exploitation, tunneling command-and-control visitors, and privilege escalation.
OwlProxy is an HTTP proxy with backdoor performance that first came to light in April 2020. SessionManager, detailed by Kaspersky final July, is a customized backdoor designed to parse the Cookie field inside inbound HTTP requests to extract the instructions issued by the attacker.
“The threat actor received access through the use of several web shells, following the attempted installation of multiple types of proxy malware and an IIS backdoor,” the researchers mentioned. “As some of the threat actor’s attempts to install malware were unsuccessful, they kept delivering new tools, showing their ability to adapt to the mitigation process.”
Author: information@thehackernews.com (The Hacker Information)
Date: 2023-09-25 02:45:00