An energetic malware marketing campaign concentrating on Latin America is allotting a brand new variant of a banking trojan known as BBToksignificantly customers in Brazil and Mexico.
“The BBTok banker has a dedicated functionality that replicates the interfaces of more than 40 Mexican and Brazilian banks, and tricks the victims into entering its 2FA code to their bank accounts or into entering their payment card number,” Test Level said in analysis printed this week.
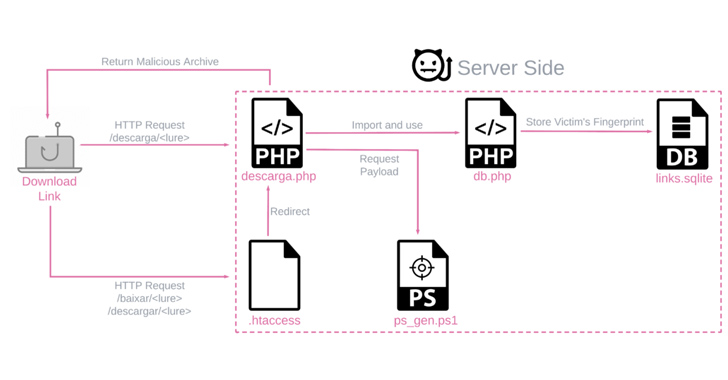
The payloads are generated by a customized server-side PowerShell script and are distinctive for every sufferer primarily based on the working system and nation, whereas being delivered by way of phishing emails that leverage quite a lot of file sorts.
BBTok is a Home windows-based banking malware that first surfaced in 2020. It is geared up with options that run the standard trojan gamut, permitting it to enumerate and kill processes, concern distant instructions, manipulate keyboard, and serve pretend login pages for banks working within the two international locations.
The assault chains themselves are pretty easy, using bogus hyperlinks or ZIP file attachments to stealthily deploy the banker retrieved from a distant server (216.250.251[.]196) whereas displaying a decoy doc to the sufferer.

However they’re additionally diversified for each Home windows 7 and Home windows 10 techniques, primarily taking steps to evade newly applied detection mechanisms similar to Antimalware Scan Interface (AMSI) that enables for scanning the machine for any threats.
Two different key strategies to fly beneath the radar are the usage of living-off-the-land binaries (LOLBins) and geofencing checks to make sure that the targets are solely from Brazil or Mexico earlier than serving the malware by way of the PowerShell script.
As soon as launched, BBTok establishes connections with a distant server to obtain instructions to simulate the safety verification pages for numerous banks.
In impersonating the interfaces of Latin American banks, the objective is to reap credential and authentication data entered by the customers to conduct account takeovers of the web financial institution accounts.
“What’s notable is the operator’s cautious approach: all banking activities are only executed upon direct command from its C2 server, and are not automatically carried out on every infected system,” the corporate mentioned.
Test Level’s evaluation of the malware has revealed a major enchancment to its obfuscation and concentrating on since 2020, increasing past Mexican banks. The presence of Spanish and Portuguese language within the supply code in addition to in phishing emails provides a touch as to the attackers’ origin.
Greater than 150 customers are estimated to have been contaminated by BBTok, primarily based on an SQLite database discovered within the server internet hosting the payload era element that data entry to the malicious software.
The concentrating on and the language factors to the risk actors probably working out of Brazil, which continues to be the epicenter of potent financially-focused malware.
AI vs. AI: Harnessing AI Defenses Against AI-Powered Risks
Able to deal with new AI-driven cybersecurity challenges? Be a part of our insightful webinar with Zscaler to deal with the rising risk of generative AI in cybersecurity.
“Although BBTok has been able to remain under the radar due to its elusive techniques and targeting victims only in Mexico and Brazil, it’s evident that it is still actively deployed,” Test Level mentioned.
“Due to its many capabilities, and its unique and creative delivery method involving LNK files, SMB and MSBuild, it still poses a danger to organizations and individuals in the region.”
The event comes because the Israeli cybersecurity firm detailed a brand new large-scale phishing marketing campaign that lately focused over 40 distinguished firms throughout a number of industries in Colombia with an final intention to deploy the Remcos RAT by way of a multi-stage an infection sequence.
“Remcos, a sophisticated ‘Swiss Army Knife’ RAT, grants attackers full control over the infected computer and can be used in a variety of attacks. Common consequences of a Remcos infection include data theft, follow-up infections, and account takeover,” Test Level said.
Author: information@thehackernews.com (The Hacker Information)
Date: 2023-09-22 10:48:00