The maintainers of the Python Package deal Index (PyPI) repository briefly suspended new person sign-ups following an inflow of malicious initiatives uploaded as a part of a typosquatting marketing campaign.
It said “new project creation and new user registration” was briefly halted to mitigate what it stated was a “malware upload campaign.” The incident was resolved 10 hours later, on March 28, 2024, at 12:56 p.m. UTC.
Software program provide chain safety agency Checkmarx stated the unidentified risk actors behind flooding the repository focused builders with typosquatted variations of fashionable packages.
“This is a multi-stage attack and the malicious payload aimed to steal crypto wallets, sensitive data from browsers (cookies, extensions data, etc.), and various credentials,” researchers Yehuda Gelb, Jossef Harush Kadouri, and Tzachi Zornstain said. “In addition, the malicious payload employed a persistence mechanism to survive reboots.”
The findings have been additionally corroborated independently by Mend.io, which noted that it detected greater than 100 malicious packages focusing on machine studying (ML) libraries reminiscent of Pytorch, Matplotlib, and Selenium.
The event comes as open-source repositories are more and more changing into an assault vector for risk actors to infiltrate enterprise environments.
Typosquatting is a well-documented assault method through which adversaries add packages with names carefully resembling their respectable counterparts (e.g., Matplotlib vs. Meals plot or tensorflow vs. tensourflow) with a view to trick unsuspecting customers into downloading them.
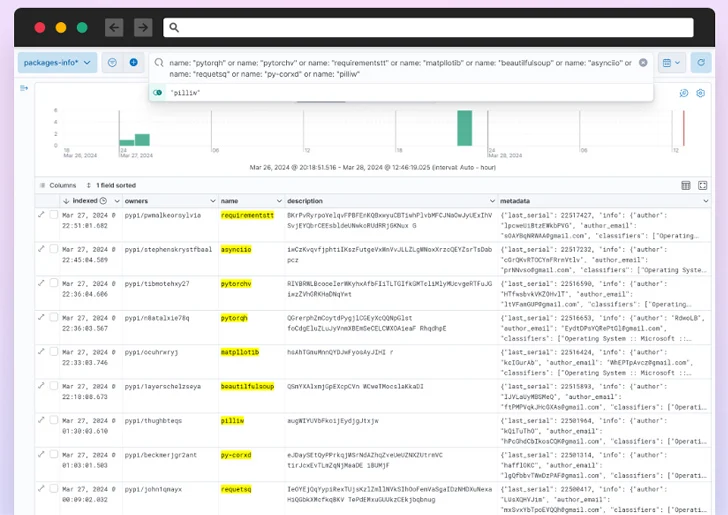
These misleading variants – totalling over 500 packages, per Verify Level – have been discovered to be uploaded from a novel account beginning March 26, 2024, suggesting that the entire course of was automated.
“The decentralized nature of the uploads, with each package attributed to a different user, complicates efforts to cross-identify these malicious entries,” the Israeli cybersecurity firm said.
Cybersecurity agency Phylum, which has additionally been tracking the same campaignstated the attackers revealed –
- 67 variations of necessities
- 38 variations of Matplotlib
- 36 variations of requests
- 35 variations of colorama
- 29 variations of tensorflow
- 28 variations of selenium
- 26 variations of BeautifulSoup
- 26 variations of PyTorch
- 20 variations of pillow
- 15 variations of asyncio
The packages, for his or her half, examine if the installer’s working system was Home windows, and in that case, proceed to obtain and execute an obfuscated payload retrieved from an actor-controlled area (“funcaptcha[.]ru”).
The malware capabilities as a stealer, exfiltrating recordsdata, Discord tokens, in addition to information from internet browsers and cryptocurrency wallets to the identical server. It additional makes an attempt to obtain a Python script (“hvnc.py”) to the Home windows Startup folder for persistence.
The event as soon as once more illustrates the escalating threat posed by software program provide chain assaults, making it essential that builders scrutinize each third-party part to make sure that it safeguards towards potential threats.
This isn’t the primary time PyPI has resorted to such a measure. In Could 2023, it temporarily disabled person sign-ups after discovering that the “volume of malicious users and malicious projects being created on the index in the past week has outpaced our ability to respond to it in a timely fashion.”
PyPI suspended new person registrations a second-time last year on December 27 for related causes. It was subsequently lifted on January 2, 2024.
Author: data@thehackernews.com (The Hacker Information)
Date: 2024-03-29 01:37:00