A brand new menace actor referred to as AtlasCross has been noticed leveraging Crimson Cross-themed phishing lures to ship two beforehand undocumented backdoors named DangerAds and AtlasAgent.
NSFOCUS Safety Labs described the adversary as having a “high technical level and cautious attack attitude,” including that “the phishing attack activity captured this time is part of the attacker’s targeted strike on specific targets and is its main means to achieve in-domain penetration.”
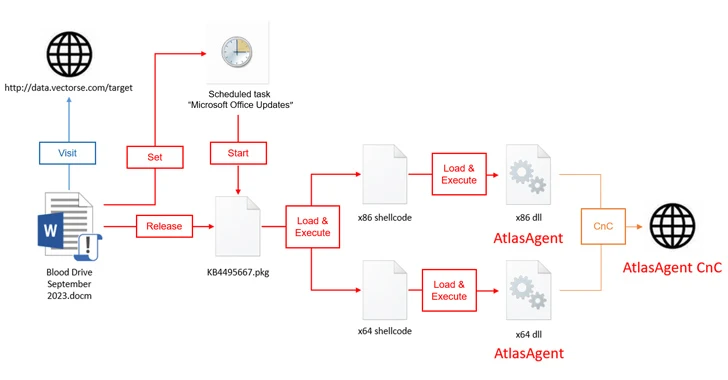
The assault chains begin with a macro-laced Microsoft doc that purports to be a couple of blood donation drive from the American Crimson Cross that, when launched, runs the malicious macro to arrange persistence, exfiltrate system metadata to a distant server (knowledge.vectorse[.]com) that is a sub-domain of a authentic web site belonging to a structural and engineering agency based mostly within the U.S.
Fight AI with AI — Battling Cyber Threats with Next-Gen AI Tools
Able to deal with new AI-driven cybersecurity challenges? Be part of our insightful webinar with Zscaler to deal with the rising menace of generative AI in cybersecurity.
It additionally extracts a file named KB4495667.pkg (codenamed DangerAds), which, subsequently acts as a loader to launch shellcode that results in the deployment of AtlasAgent, a C++ malware able to gathering system data, shellcode operation, and working instructions to acquire a reverse shell in addition to inject code right into a thread within the specified course of.
Each AtlasAgent and DangerAds incorporate evasive options to make it much less prone to be found by safety instruments.
AtlasCross is suspected to have breached public community hosts by exploiting identified safety vulnerabilities and turning them into command-and-control (C2) servers. NSFOCUS stated it recognized 12 completely different compromised servers within the U.S.
The true identification of AtlasCross and its backers at the moment stays a puzzle.
“At this current stage, AtlasCross has a relatively limited scope of activity, primarily focusing on targeted attacks against specific hosts within a network domain,” the corporate stated. “However, the attack processes they employ are highly robust and mature.”
Author: data@thehackernews.com (The Hacker Information)
Date: 2023-09-27 10:42:00