We beforehand checked out common server authentication issues we see in code assessment and provided tricks to keep away from them. In the event you adopted these options, it is best to have improved your server authentication strategies and might guarantee all of your incoming requests have a validated person hooked up.
Subsequent, we’ll talk about some widespread pitfalls for extending belief to customers to allow them to solely entry assets they’re speculated to. We’ll use the same instance to the final article. Think about we’re utilizing a hypothetical Python/Django app, which might apply to virtually any language and internet framework.
For this situation, let’s say we need to construct an API that allows a person to get the contents of one in all their personal repositories. Beneath is an instance of how somebody would possibly go about constructing this API.
Let’s say they set the route for the API to have a sample like this (the place user_id and repo_name are parameters handed within the request):
Bear in mind to Examine for Permissions
Let’s write a naive implementation of this API we described above:
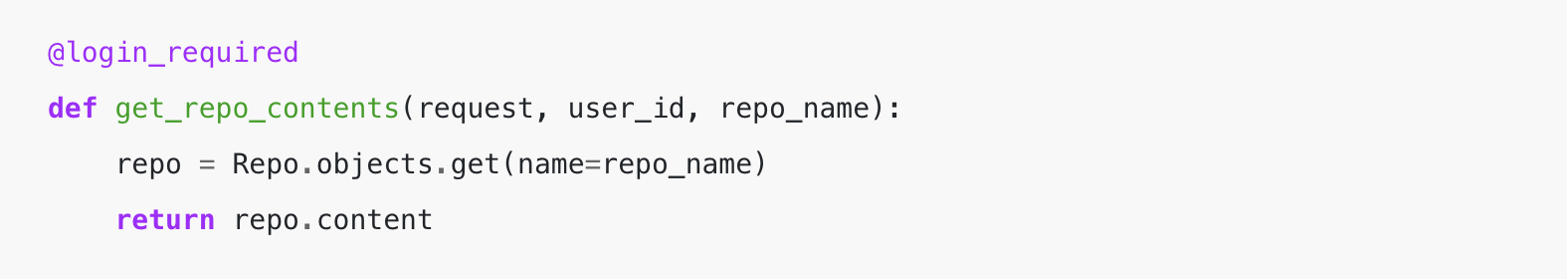
Within the above instance, there are not any permissions checks in place. The requesting person might be any logged person as we’re simply blindly trying up the repository and returning contents. Skipping the permission examine permits any person in your system to see now the contents of every other person’s personal repository.
This time let’s add a permission examine to the request:
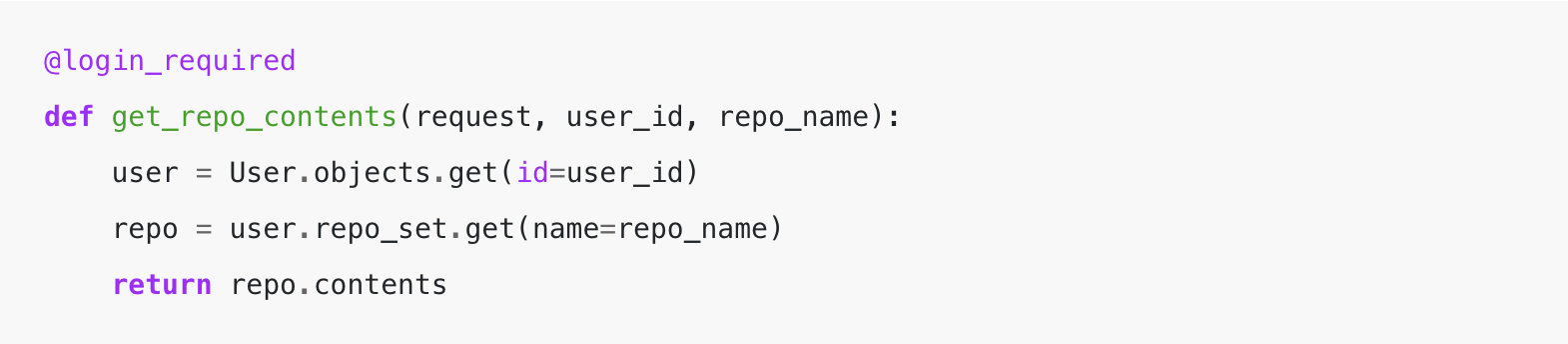
At first look, this instance appears like this might correctly examine a person’s permissions.
The API requires authentication, and we take the user_id handed after which filtered the repo objects to solely embody these which might be associated/owned by the person earlier than we glance up the repo_name.
This filtering signifies that for this person we’re trying up, we are going to solely acknowledge the existence of a repo whether it is of their set of repos they’ve permissions to entry. In any other case, it would throw a 404-type error.
Whereas this instance above appears prefer it now secures entry, there’s a widespread drawback. We aren’t extending the belief of our authentication that we labored so arduous to get right. We’re authenticating “a user,” but the route URL contains one other person parameter in it that we’re utilizing for the permissions examine.
This lack of additional authentication signifies that an attacker might see the contents of different person’s personal repositories by making a single person account, guess user_ids of different customers, and name this API.
Extending Your Belief
Probably the greatest approaches for permissions I describe as “extending your trust.” This implies to begin from a spot of belief, which is your authenticated person for the request. Then construct out queries/relations from the person to no matter object you are attempting to entry. Every step of the best way, you solely grant entry to issues the requesting person has entry to or “owns.”
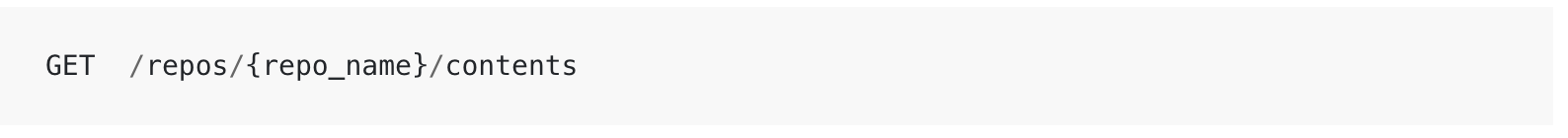
The actual fact we included the user_id within the API URL ought to be a fast code-smell for points like this. Until you’re constructing a publicly shareable system, you shouldn’t normally want to incorporate this within the API URL.
Due to this, we should always replace the API URL to appear to be this:
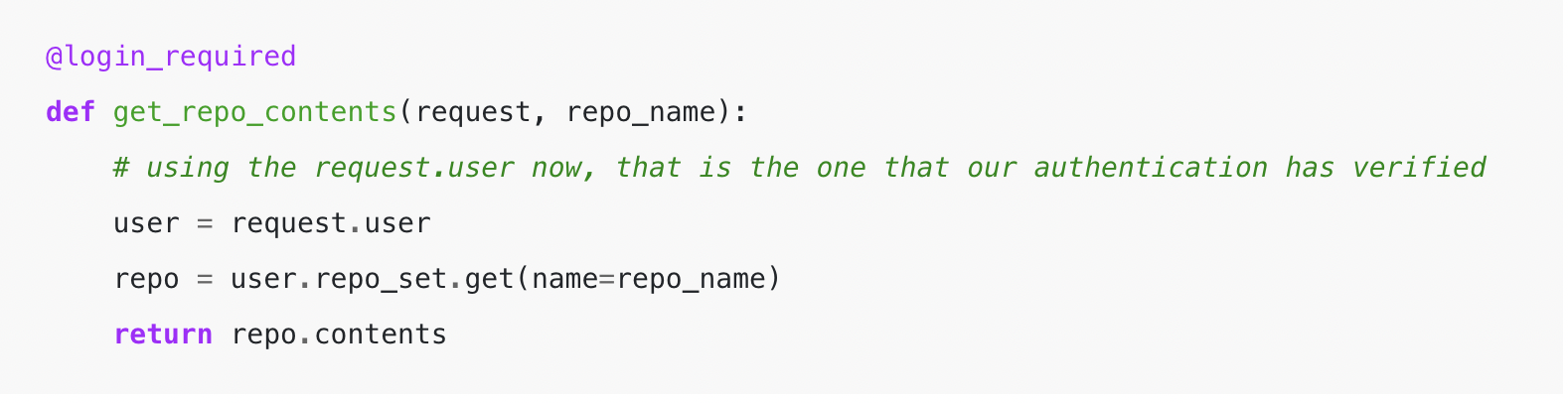
As you may see above, we’re taking the request.person and lengthening from there to get our repos that we now have permission to entry.
Further Layers of Protection
These examples present how simple it’s to write down code that appears like it’s doing all of the steps of authorization when it has a number of attainable entry points. To additional defend your assets, it is best to try so as to add a number of layers of protection on prime of the options above.
A technique is to make use of a safe id, resembling a randomly generated UUID string (version 4 UUID) for figuring out customers. If somebody unintentionally launched a permissions error and used the sort of UUIDs as a substitute of ids, the floor space of publicity is probably not as dangerous.
For instance, with auto-incrementing user_idsan attacker might attempt user_ids beginning at 1, incrementally improve to 2, then 3, and so forth till they discovered a user_id with permission. Then again, if you happen to use UUIDs, they must know the precise UUID for the person beforehand, as guessing a random string is close to unimaginable. Nonetheless, this could simply be used as an additional layer of protection and isn’t safe sufficient by itself to outline permissions as it’s attainable that you would leak the UUIDs to different customers in another APIs.
Additionally, with regular unit take a look at protection, permissions and authorization points are difficult to catch. It’s possible that you probably have unit assessments, you’re utilizing faux ids that will cross even with the problems above. So it’s a good suggestion so as to add assessments representing circumstances the place an attacker is making an attempt to interrupt your permissions, as proven within the examples above.
Even if you happen to miss a number of the above protections, code assessment is among the finest locations to catch these sorts of points. A recent set of eyes can learn over your code and is extra prone to discover issues that appear misplaced and result in some of these vulnerabilities.
This put up was initially revealed on the PullRequest web site. On April twenty eighth, 2022, HackerOne acquired PullRequest to assist energy developer-first safety testing options.
Observe the put up creator right here: Tyler Mann (@syncMutex) | Twitter
The most recent Tweets from Tyler Mann (@syncMutex). Engineering @ HackerOne Former Co-Founder / CTO @pullrequestcom. Austin, TX
Author: Tyler Mann
Date: 2022-06-23 12:00:00



