A financially motivated marketing campaign has been concentrating on on-line cost companies within the Asia Pacific, North America, and Latin America with internet skimmers for greater than a yr.
The BlackBerry Analysis and Intelligence Workforce is monitoring the exercise underneath the title Silent Skimmerattributing it to an actor who’s educated within the Chinese language language. Outstanding victims embody on-line companies and point-of-sale (PoS) service suppliers.
“The campaign operators exploit vulnerabilities in web applications, particularly those hosted on Internet Information Services (IIS),” the Canadian cybersecurity agency said. “Their primary objective is to compromise the payment checkout page, and swipe visitors’ sensitive payment data.”
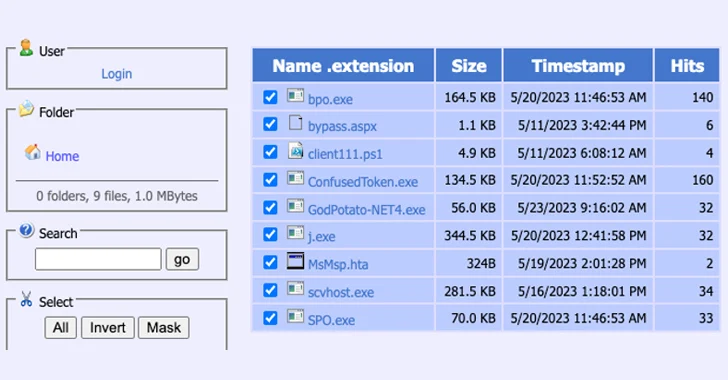
A profitable preliminary foothold is adopted by the risk actors leveraging a number of open-source instruments and living-off-the-land (LotL) methods for privilege escalation, post-exploitation, and code execution.
The assault chain results in the deployment of a PowerShell-based distant entry trojan (server.ps1) that enables for remotely controlling the host, which, in flip, connects to a distant server that hosts extra utilities, together with downloading scripts, reverse proxies and Cobalt Strike beacons.
The top aim of the intrusion, per BlackBerry, is to infiltrate the online server and drop a scraper within the cost checkout service by the use of an internet shell and stealthily seize the monetary info entered by victims on the web page.
An examination of the adversary’s infrastructure reveals that the digital personal servers (VPS) used for command-and-control (C2) are chosen based mostly on the geolocation of the victims in an effort to evade detection.
The range of industries and areas focused, coupled with the sort of servers breached, factors to an opportunistic marketing campaign reasonably than a deliberate strategy.
“The attacker focuses predominantly on regional websites that collect payment data, taking advantage of vulnerabilities in commonly used technologies to gain unauthorized access and retrieve sensitive payment information entered into or stored on the site,” BlackBerry stated.
The disclosure comes as Sophos disclosed particulars of a pig butchering scam by which potential targets are lured into investing in bogus cryptocurrency funding schemes after being approached on courting apps like MeetMe, netting the actors thousands and thousands in illicit earnings.
What units the most recent operation aside is the usage of liquidity mining lures, promising customers common earnings at excessive charges of return for funding in a liquidity pool, the place the digital property are parked to facilitate trades on decentralized exchanges.
“These scams require no malware on the target’s device, and no ‘hacking’ of any sort other than fraudulent websites and social engineering — convincing targets to connect their wallet to an Ethereum smart contract that gives the scammers permission to empty the wallet,” safety researcher Sean Gallagher said.
Author: information@thehackernews.com (The Hacker Information)
Date: 2023-10-02 07:20:00