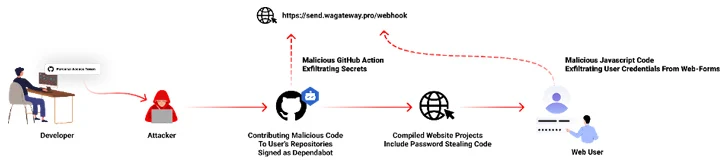
A brand new malicious marketing campaign has been noticed hijacking GitHub accounts and committing malicious code disguised as Dependabot contributions with an purpose to steal passwords from builders.
“The malicious code exfiltrates the GitHub project’s defined secrets to a malicious C2 server and modify any existing javascript files in the attacked project with a web-form password-stealer malware code effecting any end-user submitting its password in a web form,” Checkmarx said in a technical report.
The malware can be designed to seize GitHub secrets and techniques and variables to a distant server by the use of a GitHub Motion.

The software program provide chain safety agency mentioned it noticed the atypical commits to a whole bunch of private and non-private GitHub repositories between July 8 and 11, 2023.
It has emerged that the victims had their GitHub private entry tokens stolen and utilized by the risk actors to make malicious code commits to customers’ repositories by posing as Dependabot.
It depends is designed to alert customers of safety vulnerabilities in a undertaking’s dependencies by mechanically generating pull requests to maintain them up-to-date.
“The attackers accessed the accounts using compromised PATs (Personal Access Token) — most likely exfiltrated silently from the victim’s development environment,” the corporate mentioned. Most compromised customers are situated in Indonesia.
Nonetheless, the precise methodology by which this theft could have taken place is at present unclear, though it is suspected that it could have concerned a rogue package inadvertently put in by the builders.
The event highlights the continued makes an attempt on a part of risk actors to poison open-source ecosystems and facilitate provide chain compromises.
That is evidenced by a brand new information exfiltration marketing campaign focusing on each npm and PyPI that makes use of as many as 39 counterfeit packages to assemble delicate machine data and transmit the main points to a distant server.
Fight AI with AI — Battling Cyber Threats with Next-Gen AI Tools
Able to sort out new AI-driven cybersecurity challenges? Be part of our insightful webinar with Zscaler to deal with the rising risk of generative AI in cybersecurity.
The modules, revealed over a number of days between September 12 and 24, 2023, show a progressive improve in complexity, scope, and obfuscation strategies, Phylum said.
The Israeli firm can be monitoring what it characterised as a big typosquat marketing campaign geared toward npm, through which 125 packages masquerading as angular and react are getting used to ship machine data to a distant Discord channel.
Nonetheless, the exercise seems to be a part of a “research project,” with the creator claiming that it is completed to “find out if any of the bug bounty programs I’m participating in gets affected by one of the packages so that I could be the first one to notify them and protect their infrastructure.”
“This is in violation of the npm Acceptable Use Policy, and these sorts of campaigns put a strain on individuals tasked with keeping these ecosystems clean,” Phylum cautioned.
Author: data@thehackernews.com (The Hacker Information)
Date: 2023-09-28 13:22:00