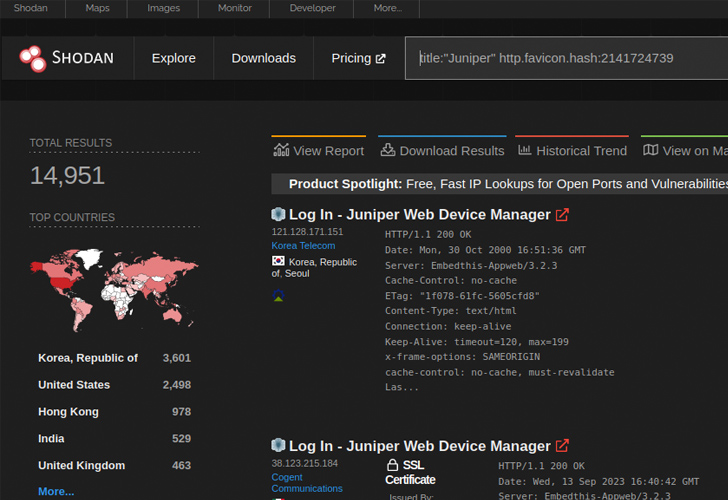
New analysis has discovered that near 12,000 internet-exposed Juniper firewall gadgets are susceptible to a just lately disclosed distant code execution flaw.
VulnCheck, which discovered a brand new exploit for CVE-2023-36845, stated it might be exploited by an “unauthenticated and remote attacker to execute arbitrary code on Juniper firewalls without creating a file on the system.”
CVE-2023-36845 refers to a medium-severity flaw within the J-Net element of Junos OS that might be weaponized by a risk actor to manage sure, vital surroundings variables. It was patched by Juniper Networks final month alongside CVE-2023-36844, CVE-2023-36846, and CVE-2023-36847 in an out-of-cycle replace.

A subsequent proof-of-concept (PoC) exploit devised by watchTowr mixed CVE-2023-36846 and CVE-2023-36845 to add a PHP file containing malicious shellcode and obtain code execution.
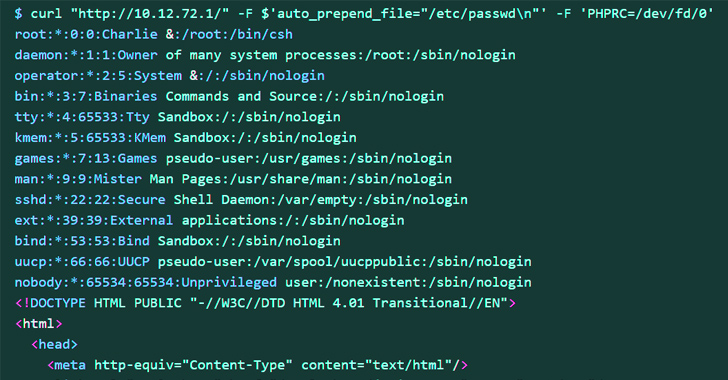
The most recent exploit, however, impacts older methods and may be written utilizing a single cURL command. Particularly, it depends on simply CVE-2023-36845 to understand the identical goal.
This, in flip, is completed through the use of the usual enter stream (aka stdin) to set the PHPRC surroundings variable to “/dev/fd/0” through a specifically crafted HTTP request, successfully turning “/dev/fd/0” right into a makeshift file, and leak delicate info.
Arbitrary code execution is then achieved by leveraging PHP’s auto_prepend_file and allow_url_include choices together with the data:// protocol wrapper.
AI vs. AI: Harnessing AI Defenses Against AI-Powered Risks
Able to sort out new AI-driven cybersecurity challenges? Be a part of our insightful webinar with Zscaler to handle the rising risk of generative AI in cybersecurity.
“Firewalls are interesting targets to APT as they help bridge into the protected network and can serve as useful hosts for C2 infrastructure,” Jacob Baines stated. “Anyone who has an unpatched Juniper firewall should examine it for signs of compromise.”
Juniper has since disclosed that it is not conscious of a profitable exploit towards its clients, however warned that it has detected exploitation makes an attempt within the wild, making it crucial that customers apply the mandatory fixes to mitigate potential threats.
Author: data@thehackernews.com (The Hacker Information)
Date: 2023-09-19 05:30:00